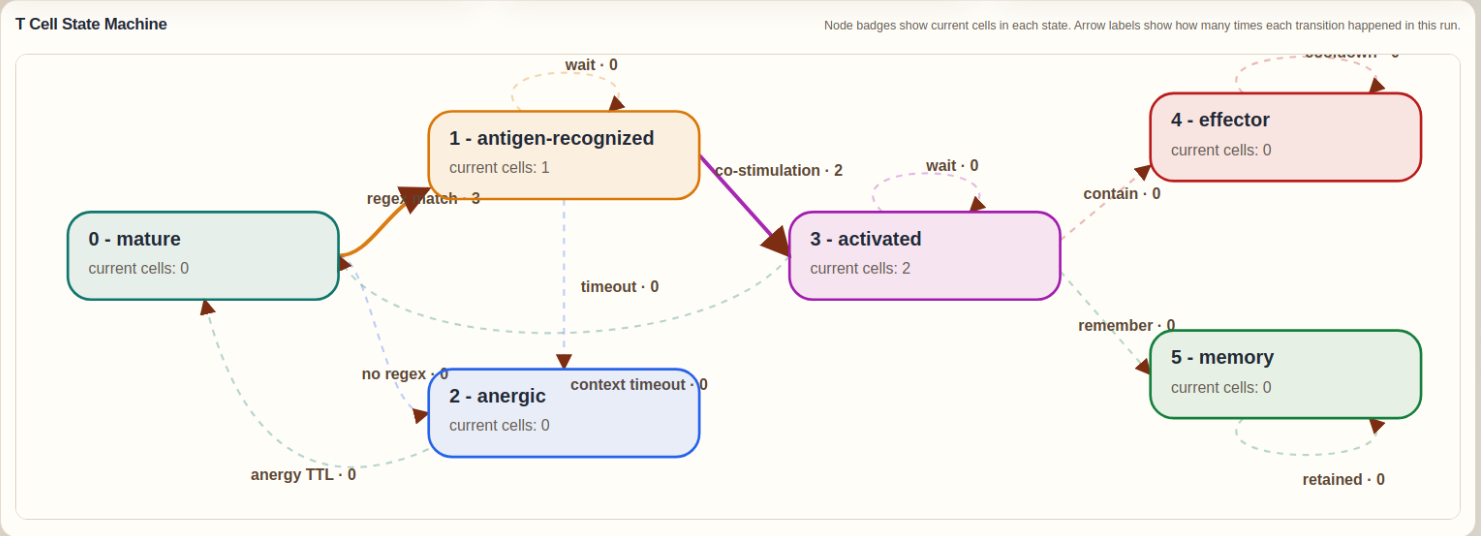
The T Cell module was created to give Slips a stateful adaptive response layer on top of its existing evidence pipeline. While the original detectors already provide the innate immune component through PAMP and DAMP evidence, the T Cell module adds antigen recognition, co-stimulation, context evaluation, tolerance, activation, effector action, and memory. It does this by extracting structured antigens from live evidence, matching them against the accepted regex repertoire generated by RegexGenerator, and then combining that recognition with the cumulative danger signaled by recent PAMP and DAMP observations. This allows Slips to move from isolated detections to a more explicit immune decision process that can decide when to ignore, when to contain, and when to remember.
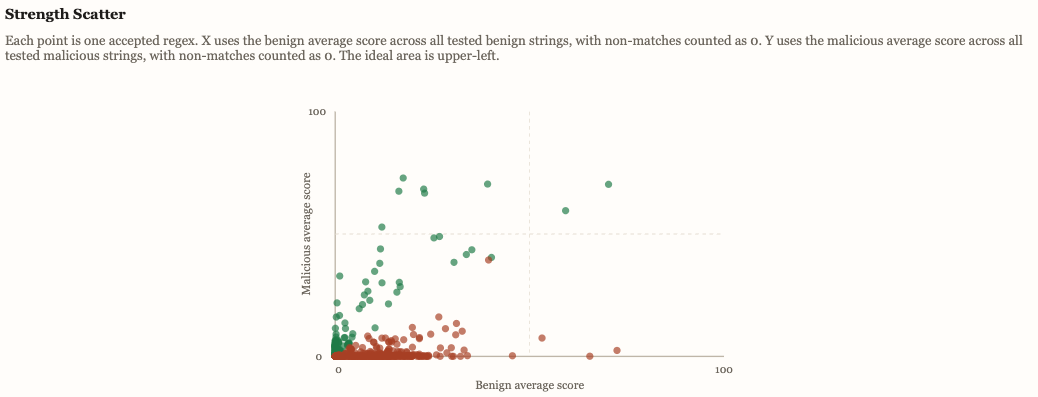
The RegexGenerator module was created to give Slips an adaptive way to discover new string-based detectors for changing indicators such as domains, URIs, filenames, TLS SNI values, and certificate common names. It continuously uses the shared LLM service to propose one regex at a time, then applies local validation and negative selection against benign corpora to reject unsafe or overly broad patterns. The accepted regexes become a reusable adaptive recognition repertoire for other modules, especially the T Cell responder.
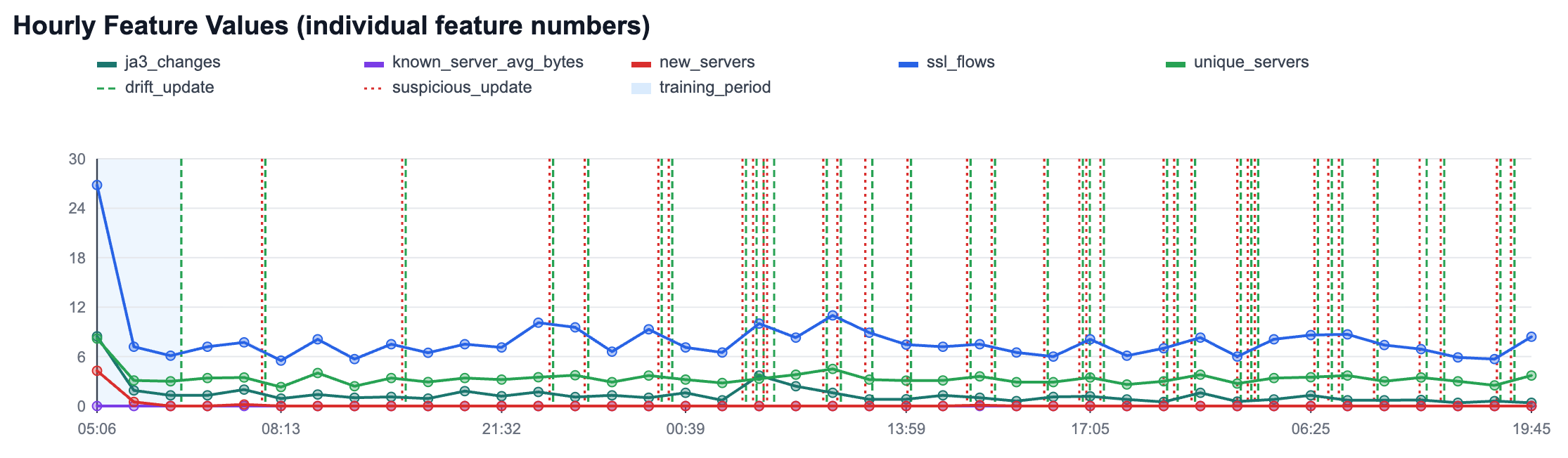
The new HTTPS anomaly detection module in Slips builds per-host adaptive baselines in traffic time, then detects deviations at two levels: per-flow (for bytes to known servers) and per-hour (for host behavior like new servers, unique servers, JA3 changes, and flow volume). It uses online statistics and z-scores for transparent scoring, plus controlled adaptation states (training_fit, drift_update, suspicious_update) to keep learning while reducing poisoning risk.
The result is explainable, operational evidence in clear human text: what changed, confidence, and why it is anomalous.
Our research identifies sixteen fundamental principles of biological immunity and translates them into cybersecurity defense architectures that emphasize multi-dimensional coordination over single- point tactics.

We are pleased to announce the publication of our latest paper, “Building adaptive and transparent cyber agents with local language models,” in the Journal of Expert Systems with Applications.
