By analyzing the activity/traffic of a large network, it is possible to spot scanning attempts potentially performed by threat actors. Scanning for the SAP NetWeaver JAVA default port increased significantly after the release of the patch for the RECON vulnerability.
IoT Malware Analysis Series. An IoT malware dropper with custom C&C channel exploiting HNAP
On February 28th, 2019 we infected one of our devices with the malware sample that most AV detect as Mirai. However, it was a bash script downloader that obtains and exacute an ARM ELF binary to attack others using the HNAP vulnerability in order to infect new bots.
ANALISIS OF CTU-MALWARE-CAPTURE-1 (ZBOT.OOWO)
CTU-MALWARE-CAPTURE-1 (ZBOT.OOWO)
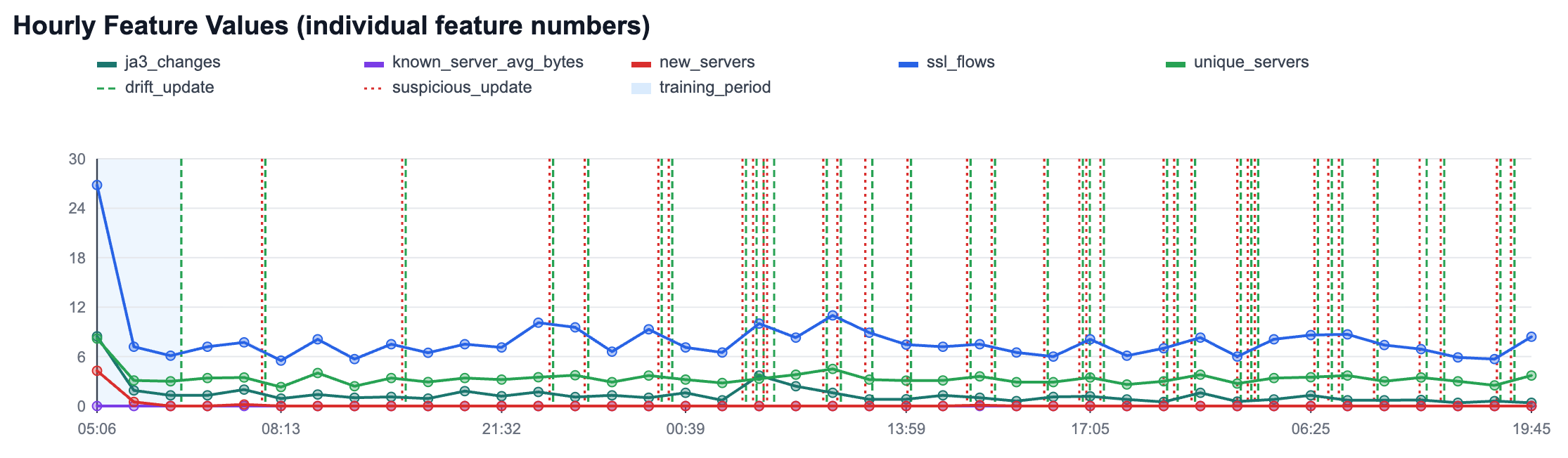
This capture was done between Thu Sep 5 15:40:07 CEST 2013 and Tue Oct 1 13:38:29 CEST 2013, having a total of 25 days and 21 hours. It corresponds to a binary with the MD5 46b3df3eaf1312f80788abd43343a9d2 of and that was classified by Kaspersky in VirusTotal as Trojan-Spy.Win32.Zbot.oowo. However we are not sure of the name.