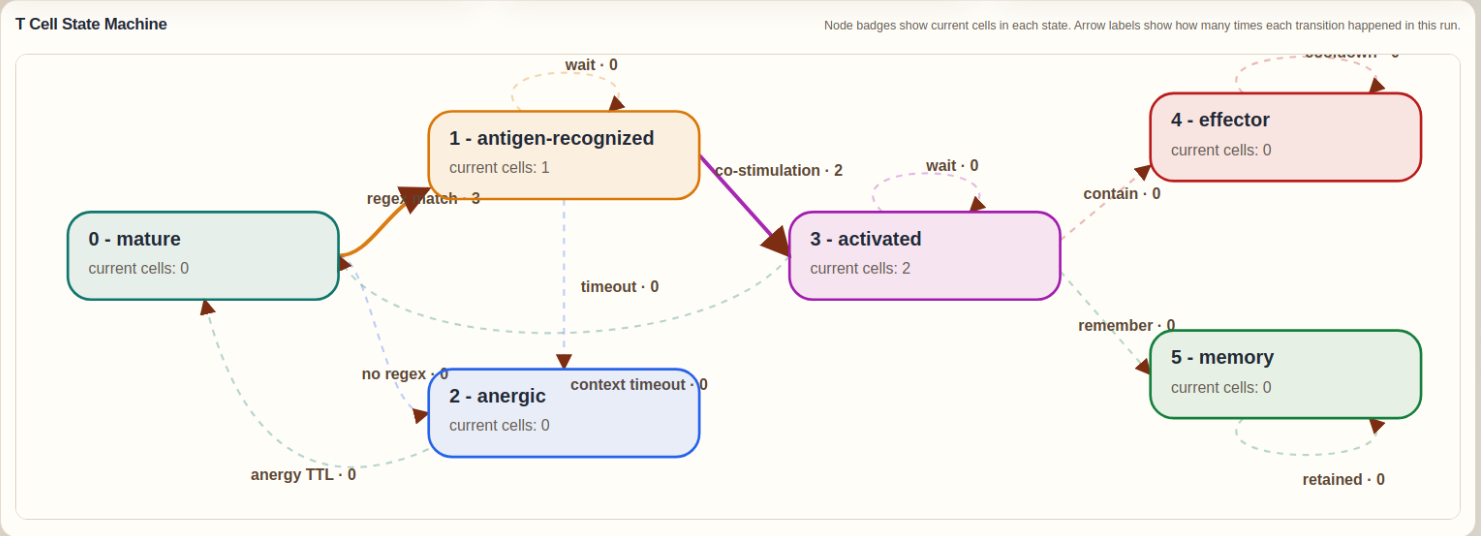
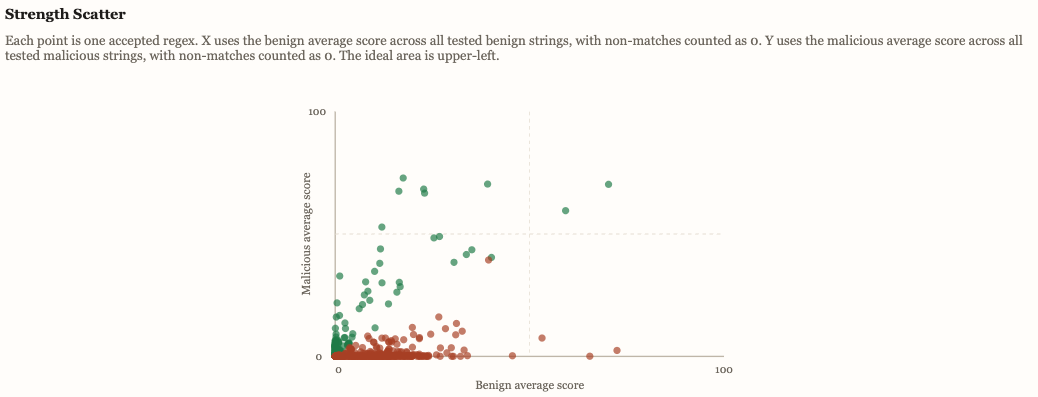
The T Cell module was created to give Slips a stateful adaptive response layer on top of its existing evidence pipeline. While the original detectors already provide the innate immune component through PAMP and DAMP evidence, the T Cell module adds antigen recognition, co-stimulation, context evaluation, tolerance, activation, effector action, and memory. It does this by extracting structured antigens from live evidence, matching them against the accepted regex repertoire generated by RegexGenerator, and then combining that recognition with the cumulative danger signaled by recent PAMP and DAMP observations. This allows Slips to move from isolated detections to a more explicit immune decision process that can decide when to ignore, when to contain, and when to remember.
New Slips version 0.8 is here!
In the last couple of months we have been busy continuing with the development of Slips, our behaviour machine learning system. And finally we published version 0.8, with crazy amount of features! You can download it from here https://github.com/stratosphereips/StratosphereLinuxIPS. And read the documentation here https://stratospherelinuxips.readthedocs.io/en/develop/.
The Attacking Active Directory Game - Can you outsmart the Machine Learning model? Help us by playing the evasion game!
The “Attacking Active Directory Game” is part of a project where our researcher Ondrej Lukas developed a way to create fake Active Directory (AD) users as honey-tokens to detect attacks. His machine learning model was trained in real AD structures and can create a complete new fake user that is strategically placed in the structure of a company.
Installing and Running Slips in Docker
The Stratosphere Linux IPs, for short Slips, is a free software intrusion prevention system that uses machine learning. Slips allows analysts to quickly sift through large network captures as well as real live traffic, highlighting what is important to analyze. The analysis we do as part of the Emergency VPN service at Civilsphere relies heavily on Slips.
Machine Learning Leaks and Where to Find Them
Machine learning systems are now ubiquitous and work well in several applications, but it is still relatively unexplored how much information they can leak. This blog post explores the most recent techniques that cause ML models to leak private data, an overview of the most important attacks, and why this type of attacks are possible in the first place.
Aposemat IoT-23: A Labeled Dataset With Malicious And Benign IoT Network Traffic
We have released the IOT23, the first dataset with real malware and benign IoT network traffic. It contains more than 300 million of labeled flows of more than 500 hours of network traffic. In this blog we explain how the dataset was created, and all the details about it.
My first summer school
Last week I had the opportunity to attend the 1st Transylvanian Deep Learning Summer School (TMLSS). It took place in Cluj, Romania and its main focus was Deep Learning and Reinforcement Learning. Here is the link to website that includes the programme and the full list of lecturers. (link)