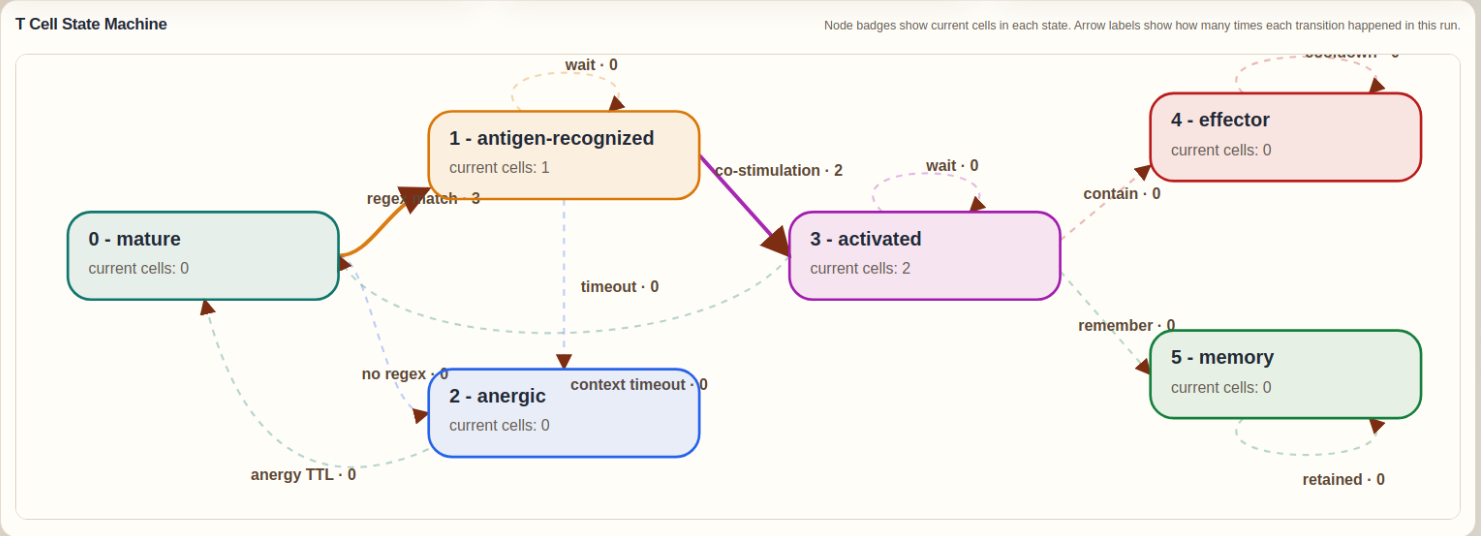
NetSecGame v0.2.0 is here. This release focuses on what matters most for reproducible AI research: deterministic episode control, a more robust simulation server, and a significantly expanded test suite. Whether you are running large-scale RL experiments or debugging a new agent, v0.2.0 makes the process more reliable.
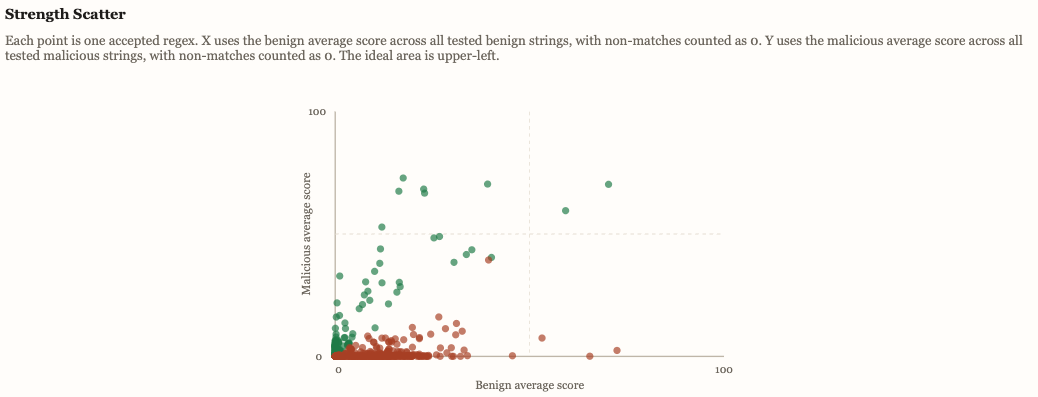
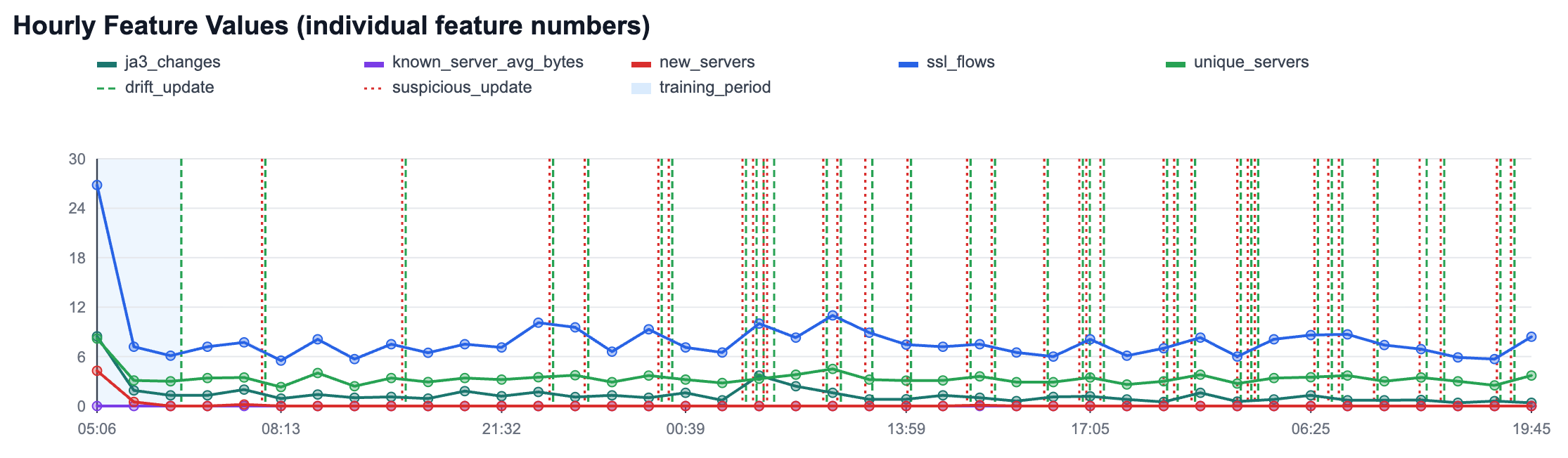
HTTPS Anomaly Detection in Slips: Adaptive Baselines for Real Traffic
The new HTTPS anomaly detection module in Slips builds per-host adaptive baselines in traffic time, then detects deviations at two levels: per-flow (for bytes to known servers) and per-hour (for host behavior like new servers, unique servers, JA3 changes, and flow volume). It uses online statistics and z-scores for transparent scoring, plus controlled adaptation states (training_fit, drift_update, suspicious_update) to keep learning while reducing poisoning risk.
The result is explainable, operational evidence in clear human text: what changed, confidence, and why it is anomalous.
Rethinking Cybersecurity Defense: Principles from Biological Immunity
Our research identifies sixteen fundamental principles of biological immunity and translates them into cybersecurity defense architectures that emphasize multi-dimensional coordination over single- point tactics.
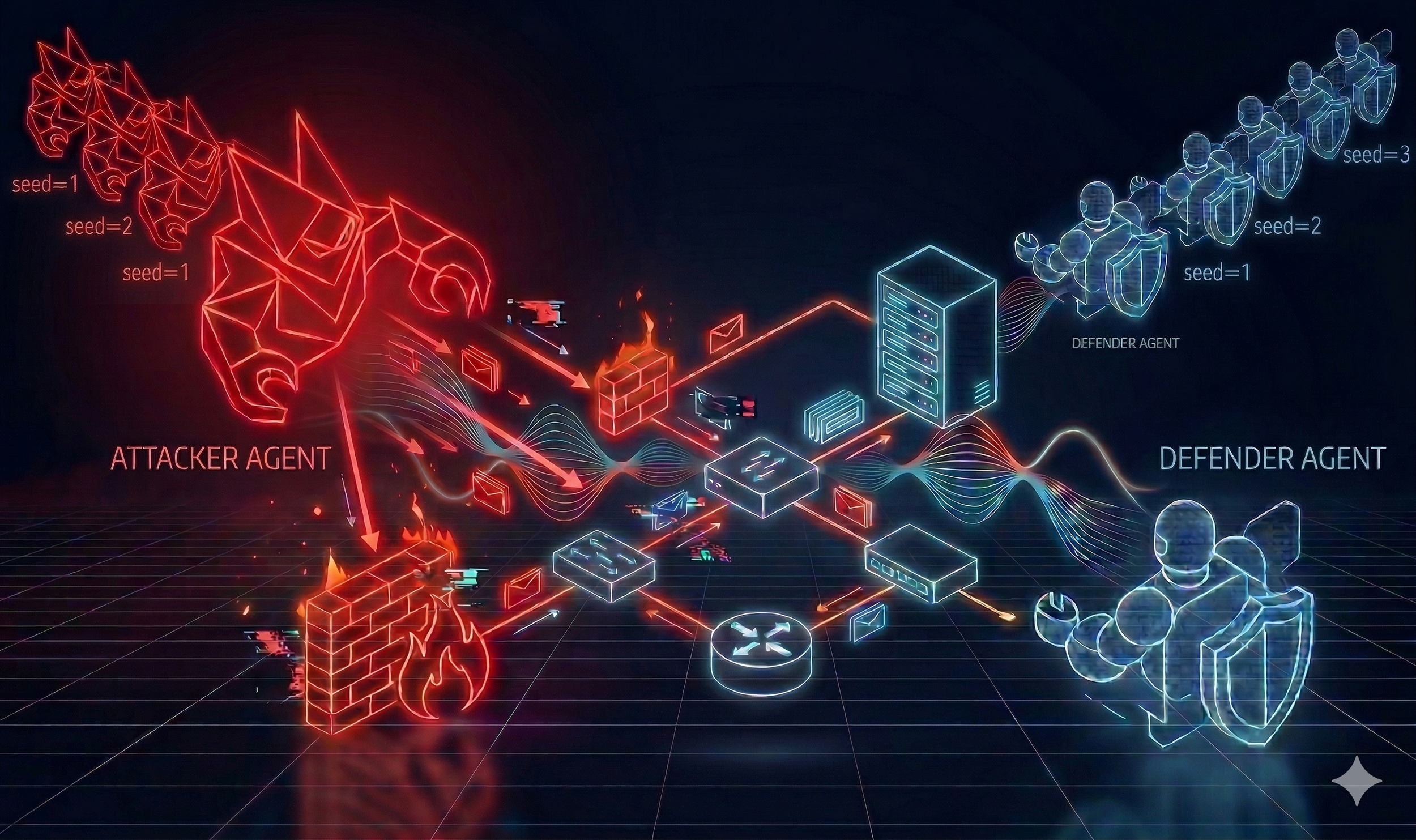
NetSecGame - A Framework for Training and Evaluating AI Agents in Network Security Environments
We are excited to announce the release of NetSecGame (NSG) v0.1.0, a framework for training and evaluating AI agents in network security environments. Developed at the Stratosphere Laboratory at CTU in Prague, NSG provides a highly configurable testbed for both offensive and defensive security tasks.
The Attacking Active Directory Game - Can you outsmart the Machine Learning model? Help us by playing the evasion game!
The “Attacking Active Directory Game” is part of a project where our researcher Ondrej Lukas developed a way to create fake Active Directory (AD) users as honey-tokens to detect attacks. His machine learning model was trained in real AD structures and can create a complete new fake user that is strategically placed in the structure of a company.
Creating "Too much noise" in DEFCON AI village CTF challenge
During DEFCON 26 the AI village hosted a jeopardy style CTF with challenges related to AI/ML and security. I thought it would be fun to create a challenge for that and I had an idea that revolved around Denoising Autoencoders (DA). The challenge was named “Too much noise” but unfortunately it was not solved by anyone during the CTF. In this blog I would like to present the idea behind it and how one could go about and solve it.