This blog post shows the analysis of a malware of the PyRation family by Tomas Nieponice as part of a 3-week winter cybersecurity internship at the Stratosphere Laboratory. The internship was done under the supervision of Assist. prof. Sebastian Garcia, PhD.
New Slips version v1.0.11 is here!
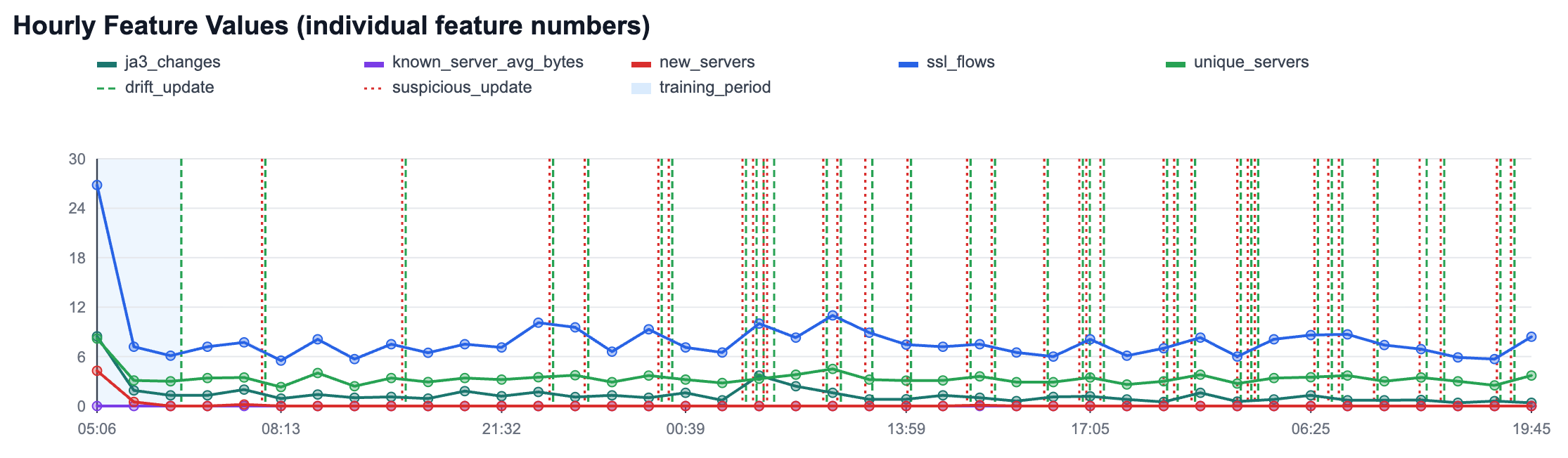
Our team is excited to share the latest news and features of Slips, our behavioral-based machine-learning intrusion detection system.
New Slips version v1.0.10 is here!
Our team is excited to share the latest news and features of Slips, our behavioral-based machine learning intrusion detection system.
New Slips version v1.0.9 is here!
Our team is excited to share the latest news and features of Slips, our behavioral-based machine learning intrusion detection system.
New Slips version v1.0.8 is here!
Our team is excited to share the latest news and features of Slips, our behavioral-based machine learning intrusion detection system.
Use Case: UptimeRobot & Stratosphere IoT Laboratory
We started working with UptimeRobot in our IoT lab, and it was like suddenly someone turned on the light.
New Slips version v1.0.7 is here!
Our team is excited to share the latest news and features of Slips, our behavioral-based machine learning intrusion detection system
"LLM in the Shell: Generative Honeypots" to be presented at ESORICS 2023 Poster Session
We are happy to announce that our researcher, Muris Sladić, will present our latest research, “LLM in the Shell: Generative Honeypots”, at the upcoming ESORICS conference poster session in The Hague, Netherlands, on Monday, September 25, 2023. Whether you plan to attend the conference or want to learn more about this research, check out our paper. Our research proposes a novel use of Large Language Models (LLMs) for dynamic on-the-fly creation and generation of more engaging honeypot environments.
Stratosphere's Slips and the AI VPN to appear at Black Hat Europe 2023 Arsenal!
We are excited to announce that two of our projects, Slips and the AI VPN, were selected to participate in the upcoming Black Hat Europe Arsenal 2023, taking place on December 6-7 in London, UK!
Generating Your Own Blocklists with the Stratosphere AIP Framework
In this blog post, we describe how to run AIP on a cloud instance server, to read from Zeek logs and generate your own blocklist feed of IPs to block. The blog is divided into five parts: first, what is AIP; second, we describe how to set up a new cloud server in Digital Ocean; third, how to configure the cloud server with Zeek running; fourth, how to prepare the environment and configurations for AIP to run; and fifth, how to run AIP and generate your own blocklists.
Google Summer of Code Updates from Week #9 (July 24th to July 28th)
With the 9th week of GSoC gone, in this blog, we bring updates on what has been happening, with news from our mentors and contributors.
Introducing Collectress: Consistent Threat Intelligence Feed Collection and Storage
This blog introduces Collectress, a new tool developed at the Stratosphere Laboratory. Collectress was born out of the need to have a certain feed for 30 days or 300 days to evaluate the feeds over time and make a reasonable comparison among feeds.
Google Summer of Code Updates from Week #8 (July 17th to July 21th)
With the 8th week of GSoC gone, in this blog, we bring updates on what has been happening, with news from our mentors and contributors.
Google Summer of Code Updates from Week #7 (July 10th to July 14th)
With the 7th week of GSoC gone, we bring updates on what has been happening in this blog, with news from our mentors and contributors.
Slips and the AI VPN presented at the 20th DIMVA Tool Arsenal in Hamburg, Germany
The Stratosphere Laboratory focus on applied research at the intersection of machine learning, cybersecurity and helping others. As part of our research and social commitment we develop free software tools that can help the community. In this blog we will recount our experience participating in the 2023 (DIMVA) Tool Arsenal with two of our tools: Slips and the AI VPN.
Google Summer of Code Updates from Week #6 (July 3rd to July 7th)
Week 6 of GSoC is finished, and we are approaching the GSoC mid-term evaluations. In this blog, we share the latest updates from our contributors and mentors.
Google Summer of Code Updates from Week #5 (June 26th to June 30th, 2023)
Week 5 of GSoC is finished, the communication was hard this week since some of the mentors were travelling, but being able to work without weekly guidance is a skill to learn.
Google Summer of Code Updates from Week #4 (June 19th to June 23th)
Week 4 of GSoC is finished, and the work continues. The contributors keep working, and we keep mentoring using a weekly sync-up meeting, Monday for task management and Discord for daily chats.
The World of Malicious IPs: Creating Blocklists from Honeypot Traffic.
A honeypot network is a security mechanism to detect and deflect potential cyber-attacks. It works by creating a decoy system that appears to be a valuable target for attackers. The honeypot is designed to lure attackers into interacting with it so that security researchers can monitor their activities and learn more about their tactics. By nature, the honeypots are hidden and do not form part of any production system. As they do not receive legitimate connections, all the interactions with the honeypots can be considered attacks.
New Slips version v1.0.6 is here!
Our team is excited to share the latest news and features of Slips, our behavioral-based machine learning intrusion detection system.